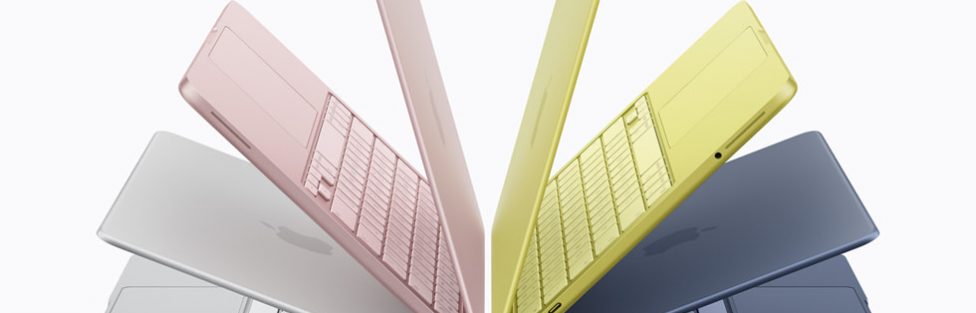
Binned Chips in Context: MacBook Neo vs. M5 MacBook Air: When comparing the MacBook Neo and the M5 MacBook Air, one of the biggest differences is not just price or form factor—it’s the underlying chip architecture. While Apple frequently uses chip … Continue Reading...
Seagate IronWolf NAS Hard Drive
We have reviewed Network Attached Storage (NAS) devices from most of the main manufacturers (read our reviews here), with more to come in the future. Regardless of which brand or … Continue Reading…
Jabra extends market leading Evolve range with Jabra 75e wireless earbuds
Jabra, a leader in professional communications and sound solutions, is extending its market-leading Evolve range of headsets for professional use with the Jabra Evolve 75e – for the first time … Continue Reading…
Epson Wins Four 2017 Golden Bridge Awards
Epson, a leading provider of innovative business solutions, recently announced it received four awards in the 9th annual Golden Bridge AwardsÒ. Epson products dominated the “New Products and Services – … Continue Reading…
From Home to Business: Synology Unveils New XS/Plus/Value-Series Product Lineup
Synology Inc. announced the official launch of new product lineup featuring: DS3018xs: Synology’s first 6-bay tower NAS with optional 10GbE and NVMe SATA SSD supports Plus-series DS918+, DS718+, and DS218+: Designed … Continue Reading…
Beware of Apple ID is Locked Scam
Several people have reported receiving an email from Apple stating that their Apple ID is locked. All indications are this is not only a scam aimed at getting your Apple … Continue Reading…
Register now for Synology Conference 2018!
Are you a Synology NAS enthusiast, love network storage devices, or just interested in winning awesome swag? If you live in the New York City and want an excuse to … Continue Reading…
Now is the best time to get a Synology a router for your home and business!
With children back at school and shorter days suitable for binging TV shows approaching, this is a great time for people to beef up their home network with one of … Continue Reading…
Introducing Logitech MX ERGO Trackball
Logitech has announced Logitech MX ERGO, a wireless trackball that sets a new standard for comfort and precision. Launching its first new innovative trackball in nearly a decade, Logitech’s MX ERGO … Continue Reading…